by Blog | Feb 10, 2024 | Cybersecurity
You cannot overstate the importance of cybersecurity. Especially in an era dominated by digital advancements. Businesses and organizations are increasingly reliant on technology to drive operations. This makes them more susceptible to cyber threats.
66% of small businesses are concerned about cybersecurity risk. Forty-seven percent lack the understanding to protect themselves. This leaves them vulnerable to the high cost of an attack.
Conveying the tangible value of cybersecurity initiatives to decision-makers can be challenging. The need for protection is clear, but executives want hard data to back up spending.
We’ll explore strategies to effectively show the concrete benefits of cybersecurity measures. These can help you make the case for stronger measures at your company. As well as help you understand how your investments return value.
How to Show the Monetary Benefits of Cybersecurity Measures
Why does demonstrating the monetary value of digital security measures pose a challenge? The benefits of cybersecurity are often indirect and preventive in nature. This differs from tangible assets with direct revenue-generating capabilities.
Investments in robust cybersecurity protocols and technologies are akin to insurance policies. They aim to mitigate potential risks rather than generate immediate financial returns. Quantifying the exact monetary value of avoided breaches or data loss can be elusive. These potential costs are hypothetical. They’re also contingent on the success of the cybersecurity measures in place.
Additionally, success is often measured by incidents that do not occur. This complicates efforts to attribute a clear monetary value. As a result, companies grapple with finding certain metrics. Ones that effectively communicate this economic impact.
Below are several ways to translate successful cybersecurity measures into tangible value.
1. Quantifying Risk Reduction
What’s one of the most compelling ways to showcase the value of cybersecurity? It’s by quantifying the risk reduction. Companies design cybersecurity initiatives to mitigate potential threats. By analyzing historical data and threat intelligence, organizations can provide concrete evidence. Evidence of how these measures have reduced the likelihood and impact of incidents.
2. Measuring Incident Response Time
The ability to respond swiftly to a cyber incident is crucial in minimizing damage. Metrics that highlight incident response time can serve as a key indicator. They can illustrate the effectiveness of cybersecurity efforts.
It’s also possible to estimate downtime costs. And then correlate those to a reduction in the time it takes to detect and respond to a security incident. This demonstrates potential savings based on faster response.
The average cost of downtime according to Pingdom is as follows:
- Up to $427 per minute (Small Business)
- Up to $16,000 per minute (Large Business)
3. Financial Impact Analysis
Cybersecurity incidents can have significant financial implications. Businesses can quantify the potential losses averted due to cybersecurity measures. Businesses do this by conducting a thorough financial impact analysis.
This can include costs associated:
- Downtime
- Data breaches
- Legal consequences
- Reputational damage
4. Monitoring Compliance Metrics
Many industries have regulatory requirements for data protection and cybersecurity. Demonstrating compliance with these regulations avoids legal consequences. It also showcases a commitment to safeguarding sensitive information. Track and report on compliance metrics. This can be another tangible way to exhibit the value of cybersecurity initiatives.
5. Employee Training Effectiveness
Human error remains a significant factor in cybersecurity incidents. Use metrics related to the effectiveness of employee training programs. This can shed light on how well the company has prepared its workforce. Prepared it to recognize and respond to potential threats. A well-trained workforce contributes directly to the company’s cybersecurity defenses.
6. User Awareness Metrics
Beyond training effectiveness, there are user awareness metrics. These gauge how well employees understand and adhere to cybersecurity policies. Use metrics such as the number of reported phishing attempts. As well as password changes and adherence to security protocols. These metrics provide insights into the human element of cybersecurity.
7. Technology ROI
Investing in advanced cybersecurity technologies is a common practice. Showcasing the return on investment (ROI) can be a powerful way to show value. Use metrics that assess the effectiveness of security technologies. Specifically, in preventing or mitigating incidents. Such as the number of blocked threats. This can highlight the tangible benefits.
8. Data Protection Metrics
For organizations handling sensitive data, metrics related to data protection are paramount. This includes monitoring the number of data breaches prevented. As well as data loss incidents and the efficacy of encryption measures. Show a strong track record in protecting sensitive information. This adds tangible value to cybersecurity initiatives.
9. Vendor Risk Management Metrics
Many organizations rely on third-party vendors for various services. Assessing and managing the cybersecurity risks associated with these vendors is crucial. Metrics related to vendor risk management showcase a comprehensive approach to cybersecurity. Such as the number of security assessments conducted. Or improvements in vendor security postures.
Schedule a Cybersecurity Assessment Today
Demonstrating the tangible value of cybersecurity starts with an assessment. One that uncovers the status of your current security measures. Knowledge is power when fostering a culture of security and resilience.
Give us a call today to schedule a chat.
—
Featured Image Credit
This Article has been Republished with Permission from The Technology Press.
by Blog | Feb 5, 2024 | Cybersecurity
The battle against cyber threats is an ongoing challenge. Unfortunately, 2023 has proven to be a watershed year for data breaches. Data compromises have surged to an all-time high in the U.S. This is based on data from the first 9 months of the year. Meaning that numbers will only end up higher for the year.
The last data breach record was set in 2021. That year, 1,862 organizations reported data compromises. Through September of 2023, that number was already over 2,100.
In Q3 of 2023, the top data compromises were:
- HCA Healthcare
- Maximus
- The Freecycle Network
- IBM Consulting
- CareSource
- Duolingo
- Tampa General Hospital
- PH Tech
This data underscores the relentless efforts of cybercriminals to exploit vulnerabilities. As well as access sensitive information. Let’s take a look at the main drivers of this increase. And the urgent need for enhanced cybersecurity measures.
1. The Size of the Surge
The numbers are staggering. Data breaches in 2023 have reached unprecedented levels. They’ve increased significantly compared to previous years. The scale and frequency of these incidents is concerning. They emphasize the evolving sophistication of cyber threats. As well as the challenges organizations face in safeguarding their digital assets.
2. Healthcare Sector Under Siege
One of the most disturbing trends is the escalating number of breaches in healthcare. Healthcare organizations are the custodians of highly sensitive patient information. As a result, they’ve become prime targets for cybercriminals. The breaches jeopardize patient privacy. They also pose serious risks to the integrity of medical records. This creates a ripple effect that can have long-lasting consequences.
3. Ransomware Reigns Supreme
Ransomware attacks continue to dominate the cybersecurity landscape. Cybercriminals are not merely after data. They are wielding the threat of encrypting valuable information. Then demanding ransom payments for its release. The sophistication of ransomware attacks has increased. Threat actors are employing advanced tactics to infiltrate networks and encrypt data. They are also using many different methods to extort organizations for financial gain.
4. Supply Chain Vulnerabilities Exposed
Modern business ecosystems have an interconnected nature. This has made supply chains a focal point for cyberattacks. The compromise of a single entity within the supply chain can have cascading effects. It can impact several organizations downstream. Cybercriminals are exploiting these interdependencies. They use vulnerabilities to gain unauthorized access to a network of interconnected businesses.
5. Emergence of Insider Threats
External threats remain a significant concern. But the rise of insider threats is adding a layer of complexity. It’s added to the already complex cybersecurity landscape. Insiders inadvertently contribute to data breaches. Whether through malicious intent or unwitting negligence. Organizations are now grappling with a challenge. They need to distinguish between legitimate user activities and potential insider threats.
6. IoT Devices as Entry Points
The proliferation of Internet of Things (IoT) devices has expanded the attack surface. There’s been an uptick in data breaches originating from compromised IoT devices. These connected endpoints range from smart home devices to industrial sensors. They are often inadequately secured. This provides cyber criminals with entry points to exploit vulnerabilities within networks.
7. Critical Infrastructure in the Crosshairs
Critical infrastructure has become a target of choice for cyber attackers. This includes energy grids, water supplies, and transportation systems. The potential consequences of a successful breach in these sectors are often financial. But that’s not all. They can also extend to public safety and national security. As cyber threats evolve, safeguarding critical infrastructure has become an urgent imperative.
8. The Role of Nation-State Actors
Geopolitical tensions have spilled into the digital realm. Nation-state actors are increasingly playing a role in sophisticated cyber campaigns. These actors are often driven by political motives. They use advanced techniques to compromise sensitive data and disrupt operations. This is to advance their strategic interests in the global cyber landscape.
9. The Need for a Paradigm Shift in Cybersecurity
The surge in data breaches underscores the need to rethink cybersecurity strategies. It’s no longer a question of if an organization will be targeted but when. Proactive measures include:
- Robust cybersecurity frameworks
- Continuous monitoring
- A culture of cyber awareness
These are essential for mitigating the risks posed by evolving cyber threats.
10. Collaboration and Information Sharing
Collaboration among organizations and information sharing within the cybersecurity community are critical. Especially as cyber threats become more sophisticated. Threat intelligence sharing enables a collective defense against common adversaries. This allows organizations to proactively fortify their defenses. They do this based on insights gained from the broader cybersecurity landscape.
Protect Your Business from Devastating Data Breaches
The surge in data breaches in 2023 serves as a stark reminder. It reminds us of the evolving and pervasive nature of cyber threats. There is an urgent need for heightened cybersecurity awareness and robust defensive measures. As well as a commitment to adapt to the ever-changing tactics of cybercriminals.
Need help protecting your business? Give us a call today to schedule a chat.
—
Featured Image Credit
This Article has been Republished with Permission from The Technology Press.
by Blog | Jan 31, 2024 | Cybersecurity
Cybersecurity has become paramount for businesses across the globe. As technology advances, so do the threats. Recognizing this, the U.S. Securities and Exchange Commission (SEC) has introduced new rules. They revolve around cybersecurity. These new requirements are set to significantly impact businesses.
These rules are a response to the growing sophistication of cyber threats. As well as the need for companies to safeguard their sensitive information.
Let’s delve into the key aspects of these new SEC regulations. We’ll review what they are and discuss how they may affect your business.
Understanding the New SEC Cybersecurity Requirements
The SEC’s new cybersecurity rules emphasize the importance of proactive cybersecurity measures. These are for businesses operating in the digital landscape. One of the central requirements is the timely reporting of cybersecurity incidents. The other is the disclosure of comprehensive cybersecurity programs.
The rules impact U.S. registered companies. As well as foreign private issuers registered with the SEC.
Reporting of Cybersecurity Incidents
The first rule is the disclosure of cybersecurity incidents deemed to be “material.” Companies disclose these on a new item 1.05 of Form 8-K.
Companies have a time limit for disclosure. This is within four days of the determination that an incident is material. The company should disclose the nature, scope, and timing of the impact. It also must include the material impact of the breach. One exception to the rule is where disclosure poses a national safety or security risk.
Disclosure of Cybersecurity Protocols
This rule requires extra information that companies must report. They report this on their annual Form 10-K filing.
The extra information companies must disclose includes:
- Their processes for assessing, identifying, and managing material risks from cybersecurity threats.
- Risks from cyber threats that have or are likely to materially affect the company
- The board of directors’ oversight of cybersecurity risks
- Management’s role and expertise in assessing and managing cybersecurity threats.
Potential Impact on Your Business
Is your business subject to these new SEC cybersecurity requirements? If it is, then it may be time for another cybersecurity assessment. Penetration tests and cybersecurity assessments identify gaps in your protocols. They help companies reduce the risk of cyber incidents and compliance failures.
Here are some of the potential areas of impact on businesses from these new SEC rules.
- Increased Compliance Burden
Businesses will now face an increased compliance burden. This is as they work to align their cybersecurity policies with the new SEC requirements. This might cause a significant overhaul of existing practices, policies, and technologies. Ensuring compliance will likely mean a large amount of time and resources. This impacts both large corporations and smaller businesses
- Focus on Incident Response
The new regulations underscore the importance of incident response plans. Businesses will need to invest in robust protocols. These are protocols to detect, respond to, and recover from cybersecurity incidents promptly. This includes having clear procedures for notifying regulatory authorities, customers, and stakeholders. This would be a notification in the event of a data breach.
- Heightened Emphasis on Vendor Management
Companies often rely on third-party vendors for various services. The SEC’s new rules emphasize the need for businesses to assess vendor practices. Meaning, how vendors handle cybersecurity. This shift in focus necessitates a comprehensive review. That review should be of existing vendor relationships. It may mean finding more secure alternatives.
- Impact on Investor Confidence
Cybersecurity breaches can erode investor confidence and damage a company’s reputation. With the SEC’s spotlight on cybersecurity, investors are likely to take note. This includes scrutinizing businesses’ security measures more closely. Companies with robust cybersecurity programs may instill greater confidence among investors. This can potentially lead to increased investments and shareholder trust.
- Innovation in Cybersecurity Technologies
As businesses strive to meet the new SEC requirements, they will seek innovation. There is bound to be a surge in the demand for advanced cybersecurity solutions. This increased demand could foster a wave of innovation in the cybersecurity sector. This could lead to the development of more effective cyber protection solutions.
The SEC Rules Bring Challenges, but Also Possibilities
The new SEC cybersecurity requirements mark a significant milestone. This is a milestone in the ongoing battle against cyber threats. While these regulations pose challenges, they also present opportunities. The opportunities are for businesses to strengthen their cybersecurity posture. As well as enhancing customer trust, and fostering investor confidence.
By embracing these changes proactively, companies can meet regulatory expectations. They can also fortify their defenses against the ever-evolving landscape of cyber threats. Adapting to these regulations will be crucial in ensuring long-term success. As well as the resilience of your business.
Need Help with Data Security Compliance?
When it comes to ensuring compliance with cybersecurity rules, it’s best to have an IT pro by your side. We know the ins and outs of compliance and can help you meet requirements affordably.
Give us a call today to schedule a chat.
—
Featured Image Credit
This Article has been Republished with Permission from The Technology Press.
by Blog | Jan 25, 2024 | Microsoft
Are you a small business owner or a freelancer who offers services online? If so, you might be wondering how to get paid by your customers in a fast and convenient way. You might have tried different payment platforms. But they often require you to switch between different apps or websites. This can be time-consuming and confusing.
There is now another option to streamline the payment process. Microsoft has launched the Teams Payments app. This is a new feature that allows you to request and receive payments from your customers. You do it within Microsoft Teams meetings.
The Teams Payments app is currently available in the United States and Canada. Subscribers to Teams Essentials and Microsoft 365 Business get it at no charge.
How Does the Teams Payment App Work?
The Teams Payments app is simple to use. You can get the app from the Microsoft AppStore. You add it to your Teams account and connect it to your preferred payment service. You can choose from:
Once you have set up the app, you can start requesting payments from your customers in Teams meetings.
How Do You Send a Payment Request?
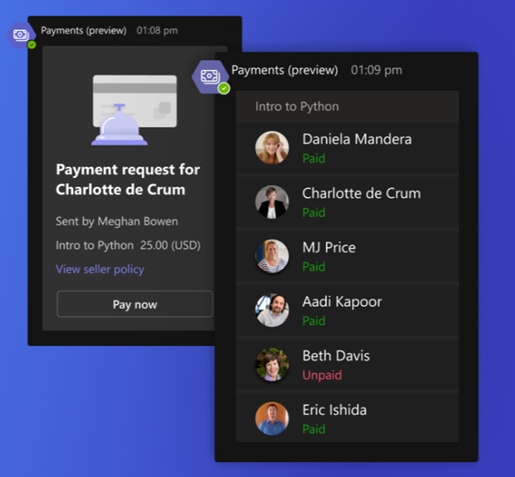
To send a payment request, you just need to open the meeting chat. Then, select the Payments icon from the messaging extensions. Then, you can fill out a simple form. It includes the amount, currency, description, and recipients of your request.
You can send the same request to several people if you want. The app will generate a card that shows the status of each payment, whether it is unpaid or paid.
Image credit: Microsoft
Your customers will see the same card in their meeting chat. They can click on the Pay Now button to complete their payment. The system will redirect them to the payment service that you have connected to the app. There, they can enter their payment details and confirm their transaction.
Once they have done that, they will see a confirmation message in the chat. You will receive a notification that your payment has been processed.
Image credit: Microsoft
Benefits of Using the Teams Payment App
The Teams Payments app has many benefits. Both for small businesses and freelancers who offer online services. Here are some of them:
It saves time and hassle.
You don’t need to switch between different apps or websites. You can easily request and receive payments from your customers. You can do everything within Teams meetings. This makes it more convenient and efficient for both parties.
It increases customer satisfaction and loyalty.
Your customers will appreciate the ease of paying you through Teams meetings. They don’t need to create an account or download an app to pay you. They can complete their transaction in a few clicks right inside the meeting.
It boosts your revenue and cash flow.
You can get paid faster and more securely by using the Teams Payments app. You don’t need to wait for invoices or checks to clear. You can receive your money within minutes of completing a service. Either directly into your bank account or PayPal account.
It enhances your professional image and credibility.
You can show your customers that you are using a reliable and trusted payment platform. One built by a well-known company that has been a technology leader for decades. You can also add a seller policy to your payment requests. Here you can specify your terms and conditions, cancellation policy, refund policy, etc.
It helps you keep track of payments.
Keeping track of payments is crucial for financial management. With the Teams Payments App, you can track transactions in real-time. You’ll receive instant notifications for successful payments. It will help you maintain a comprehensive record of your financial interactions.
It’s seamlessly integrated with Microsoft 365.
The Teams Payments App seamlessly integrates with Microsoft 365. You can leverage the power of Microsoft’s ecosystem. Using it to manage your communications, collaborations, and payments together. No need for more logins or complicated setups – it’s all within one platform.
It increases productivity.
Efficiency is the key to productivity. You reduce the time spent on payment-related tasks by integrating Payments into Teams. This efficiency translates into increased productivity. It allows you and your team to focus on core business activities and driving growth.
The Teams Payments app marks a significant leap in digital business transactions. By leveraging this powerful tool, you’re simplifying payments. You’re also enhancing customer experiences, ensuring data security, and boosting productivity.
We Can Help You Get More Out of Microsoft 365
The Teams Payments app is a great way to simplify and streamline your payment process. It can help you save time, increase customer satisfaction, and boost revenue.
Need help with this or other Microsoft 365 tools? Our experts can work with you to help you make the most out of your Microsoft subscription.
Give us a call today to schedule a chat.
—
Featured Image Credit
This Article has been Republished with Permission from The Technology Press.
by Blog | Jan 20, 2024 | Cybersecurity
The global cost of a data breach last year was USD $4.45 million. This is an increase of 15% over three years. As we step into 2024, it’s crucial to be aware of emerging technology threats. Ones that could potentially disrupt and harm your business.
Technology is evolving at a rapid pace. It’s bringing new opportunities and challenges for businesses and individuals alike. Not all technology is benign. Some innovations can pose serious threats to our digital security, privacy, and safety.
In this article, we’ll highlight some emerging technology threats to be aware of in 2024 and beyond.
Data Poisoning Attacks
Data poisoning involves corrupting datasets used to train AI models. By injecting malicious data, attackers can skew algorithms’ outcomes. This could lead to incorrect decisions in critical sectors like healthcare or finance. Some actions are vital in countering this insidious threat. These include protecting training data integrity and implementing robust validation mechanisms.
Businesses should use AI-generated data cautiously. It should be heavily augmented by human intelligence and data from other sources.
5G Network Vulnerabilities
The widespread adoption of 5G technology introduces new attack surfaces. With an increased number of connected devices, the attack vector broadens. IoT devices, reliant on 5G networks, might become targets for cyberattacks. Securing these devices and implementing strong network protocols is imperative. Especially to prevent large-scale attacks.
Ensure your business has a robust mobile device management strategy. Mobile is taking over much of the workload Organizations should properly track and manage how these devices access business data.
Quantum Computing Vulnerabilities
Quantum computing, the herald of unprecedented computational power, also poses a threat. Its immense processing capabilities could crack currently secure encryption methods. Hackers might exploit this power to access sensitive data. This emphasizes the need for quantum-resistant encryption techniques to safeguard digital information.
Artificial Intelligence (AI) Manipulation
AI, while transformative, can be manipulated. Cybercriminals might exploit AI algorithms to spread misinformation. They are already creating convincing deepfakes and automating phishing attacks. Vigilance is essential as AI-driven threats become more sophisticated. It demands robust detection mechanisms to discern genuine from malicious AI-generated content.
Augmented Reality (AR) and Virtual Reality (VR) Exploits
AR and VR technologies offer immersive experiences. But they also present new vulnerabilities. Cybercriminals might exploit these platforms to deceive users, leading to real-world consequences.
Ensuring the security of AR and VR applications is crucial. Especially to prevent user manipulation and privacy breaches. This is very true in sectors like gaming, education, and healthcare.
Ransomware Evolves
Ransomware attacks have evolved beyond simple data encryption. Threat actors now use double extortion tactics. They steal sensitive data before encrypting files. If victims refuse to pay, hackers leak or sell this data, causing reputational damage.
Some defenses against this evolved ransomware threat include:
- Robust backup solutions
- Regular cybersecurity training
- Proactive threat hunting
Supply Chain Attacks Persist
Supply chain attacks remain a persistent threat. Cybercriminals infiltrate third-party vendors or software providers to compromise larger targets. Strengthening supply chain cybersecurity is critical in preventing cascading cyber incidents. Businesses can do this through rigorous vendor assessments, multi-factor authentication, and continuous monitoring.
Biometric Data Vulnerability
Biometric authentication methods, such as fingerprints or facial recognition, are becoming commonplace. But users can’t change biometric data once compromised, like they can passwords. Protect biometric data through secure encryption. Ensure that service providers follow strict privacy regulations. These are paramount to preventing identity theft and fraud.
Advanced Phishing Attacks
Phishing attacks are one of the oldest and most common forms of cyberattacks. These attacks are becoming more sophisticated and targeted thanks to AI. For example, hackers customize spear phishing attacks to a specific individual or organization. They do this based on online personal or professional information.
Another example is vishing attacks. These use voice calls or voice assistants to impersonate legitimate entities. They convincingly persuade victims to take certain actions.
Ongoing employee phishing training is vital. As well as automated solutions to detect and defend against phishing threats.
Tips for Defending Against These Threats
As technology evolves, so do the threats that we face. Thus, it’s important to be vigilant and proactive. Here are some tips that can help:
- Educate yourself and others about the latest technology threats.
- Use strong passwords and multi-factor authentication for all online accounts.
- Update your software and devices regularly to fix any security vulnerabilities.
- Avoid clicking on suspicious links or attachments in emails or messages.
- Verify the identity and legitimacy of any callers or senders. Do this before providing any information or taking any actions.
- Back up your data regularly to prevent data loss in case of a cyberattack.
- Invest in a reliable cyber insurance policy. One that covers your specific needs and risks.
- Report any suspicious or malicious activity to the relevant authorities.
Need Help Ensuring Your Cybersecurity is Ready for 2024?
Last year’s solutions might not be enough to protect against this year’s threats. Don’t leave your security at risk. We can help you with a thorough cybersecurity assessment, so you know where you stand.
Contact us today to schedule a chat.
—
Featured Image Credit
This Article has been Republished with Permission from The Technology Press.